Securing The Mind of Machines
Attacking and Defending Gen AI

Search for a command to run...
Articles tagged with #redteaming
Attacking and Defending Gen AI

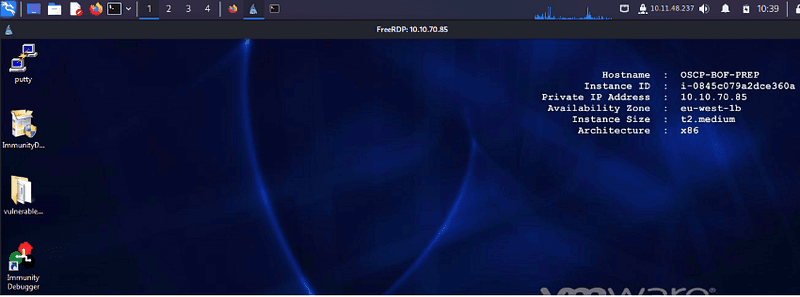
OVERFLOW focus on oscp.exe
Crafting a thorough reconnaissance strategy involves harnessing SSL/TLS certificate data from the internet to empower Bug Bounty Hunters, Pentesters, Red Teamers, and Blue Teamers. Through systematic web scraping of SSL/TLS certificates and structuri...
Step-by-step Active directory enumeration guide after getting an initial foothold
Introduction: Hello, fellow cybersecurity enthusiasts! Today, we're delving into the world of Red Team Engagements – a simulated cybersecurity challenge where ethical hacking takes center stage. Our journey begins with a look at the essential startin...
Mastering Reconnaissance: A Comprehensive Guide for Subdomain Enumeration, HTTP Probing, and Technology Stack Analysis