Peeling Back the Layers: Unmasking Hidden Secrets in JavaScript Code

Hey there! Today, let's go on a little adventure into the world of website secrets. Imagine this: if you add ?_debug=1 to the end of a JavaScript(.js) page's address, it's like unlocking a hidden door. We'll explore a cool security trick that makes a regular web address spill the beans on hidden comments and cool stuff.
The Hacker's Arsenal: ?_debug=1 Unleashed -
Imagine stumbling upon a URL like https://test.com/dist/js/validate.js?_debug=1. A harmless-looking query parameter, right? Yet, when injected with this unsuspecting flag, the JavaScript file eagerly exposes its hidden comments and debugging artifacts.
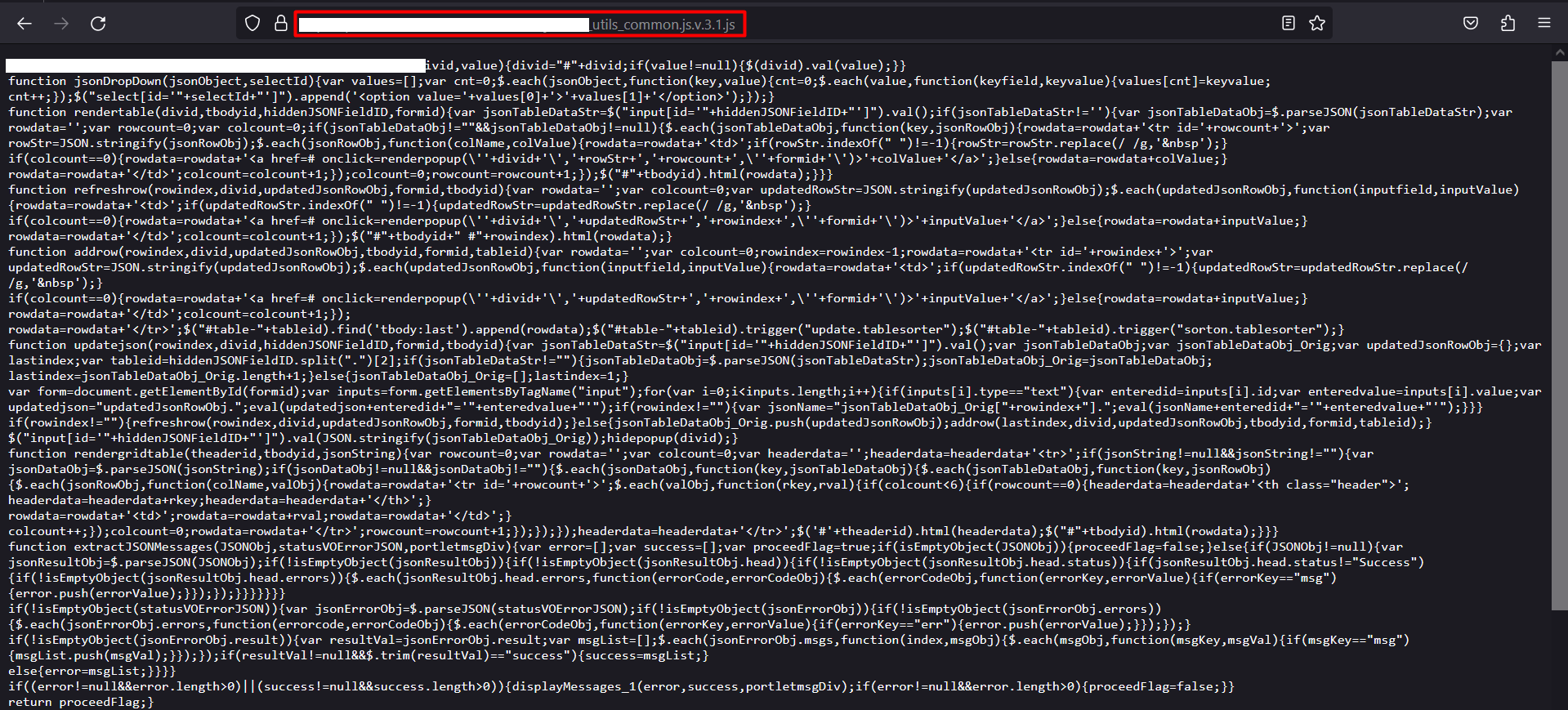
In below image you can see that how normal .js file looks when visited.
Now let's add ?_debug=1 at the end of the URL.
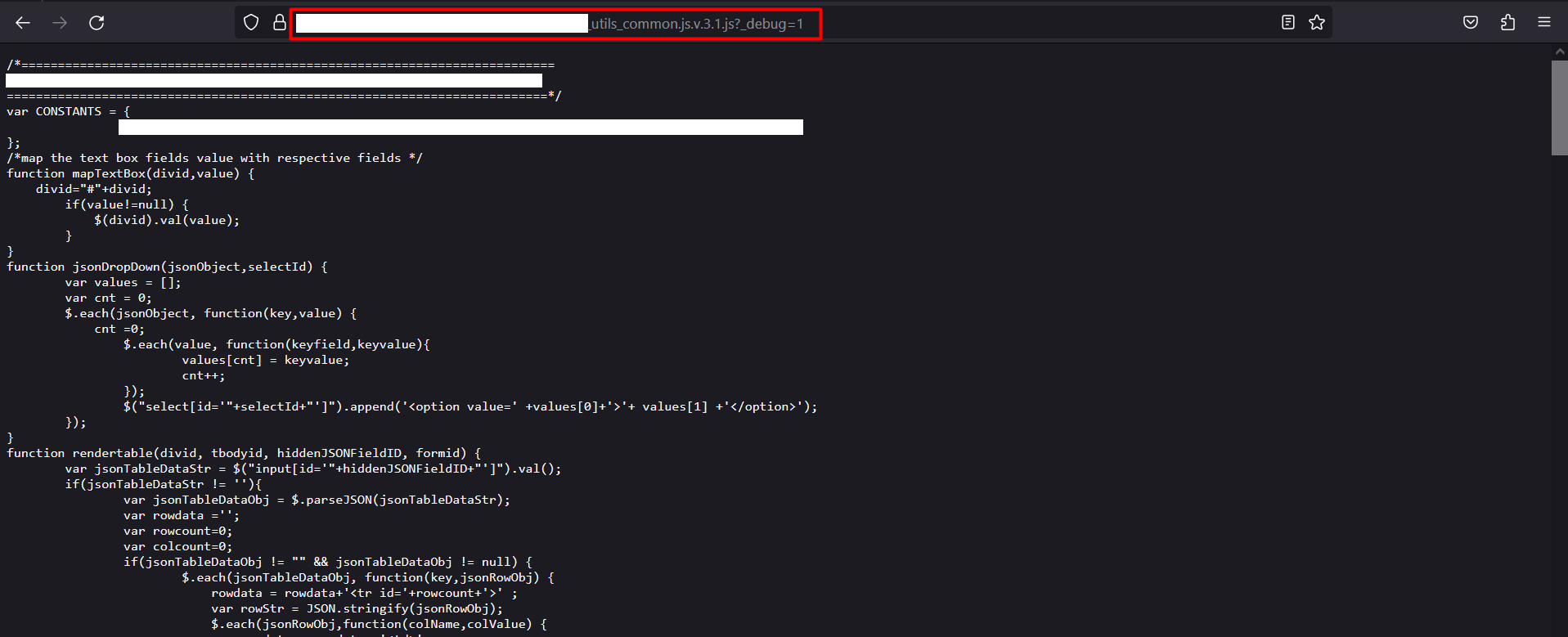
You'll notice that the JavaScript file reveals hidden comments.
(**Note - This may not work consistently. My hunch is that it should work when the debugging mode is turned on in the JavaScript file.)
The Unseen Risks
From a hacker's perspective, these hidden comments can be a gateway to understanding the inner workings of an application. It may reveal APIs, authentication mechanisms, or other delicate details, turning what seems like harmless information into a potential roadmap for an attack.
Mitigating the Risk: A Call to Action
Code Sanitization: Developers, let's adopt a meticulous approach to code sanitization. Strip away unnecessary comments and debugging artifacts before deploying code to production.
Server Configuration: Configure servers to disregard debugging flags or query parameters in production environments. Limit access to sensitive files and directories.
Educating Developers: Developers, remain vigilant. Understand the potential risks associated with n comments and encourage best practices for secure coding within your teams.
![Lecture 4 - Rediscovering Process Scheduling [Part - 1]](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1765604682888%2F80e6cf20-aded-4aac-8c75-affdd35615b2.jpeg&w=3840&q=75)
![Lecture 3 - Reinventing MMU [Part - 2]](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1763234243271%2F6bb1c737-9def-4975-a06d-7ca59791c881.png&w=3840&q=75)