August Highlights
August covered Networking Basics and Hardware Hacking
Network Basics — Vishal Vaishishth
View the slide deck for this talk here
Evolution of communication systems
Marconi (wireless telegraphy) → One-way radio → Two-way radio (interactive comms) → Digital networks (Ethernet frames, VoIP, etc.)
Guglielmo Marconi → credited with inventing wireless telegraphy (early radio), which was one-way communication (just sending signals).
Later, radio tech evolved into two-way communication (walkie-talkies, mobile phones, etc.) where both ends could talk.
Then we moved into digital communication → carrying not just analog voice but also data.
Today, even voice calls are chopped into frames/packets (like Ethernet frames in computer networks) when sent over digital/VoIP systems.
OSI Layer

Physical Layer
The Physical Layer (Layer 1) is responsible for transmitting raw bits over physical media.
Supports various transmission media:
Wires/Cables: Copper (Ethernet CAT5/6/7), Coaxial
Optical Fiber: High-speed long-distance communication (up to 58 Gbps with Ethernet over fiber)
Radio Waves: Wireless transmission for WiFi, Bluetooth, and cellular networks.
WiFi is actually Layer 2 (Data Link), but it relies on radio waves as the physical medium.
Key protocols at Layer 1: IDE, SCSI, Ethernet physical specifications.
Ethernet uses packet switching rather than circuit switching:
Packet switching sends data in discrete frames, making networks more flexible.
Circuit switching requires pre-allocated bandwidth for the duration of the communication, which is less efficient for shared networks.
Layer 1 also defines electrical/optical signal standards, connector types, and transmission speeds
Data Link Layer
The Data Link Layer (Layer 2) operates on top of the Physical Layer, ensuring devices can communicate reliably over physical media.
Compatibility is crucial: Protocols are needed so devices from different manufacturers can exchange data.
Standard Ethernet Frame: Encapsulates data for Layer 2 transmission.
MAC Address (Media Access Control):
Needed to identify devices on the same network.
If only two devices are connected on a single cable, addresses aren’t required.
When networks scale beyond two devices, MAC addresses allow correct packet delivery.
Originally sufficient for small, room-scale networks; now critical for larger, multi-device environments.
Address Management:
Managed at Layer 2 (MAC) and Layer 3 (IP).
DHCP on routers assigns IP addresses; devices cannot safely overwrite these without risk.
Why not just MAC?
MAC addresses are not extensible beyond local networks.
They are hardware-burned, making replacement difficult.
IP addresses are required for network-wide routing and scalability.
ARP Protocol (Address Resolution Protocol):
Maps IP addresses to MAC addresses for local communication.
Vulnerable to ARP spoofing and cache poisoning attacks.
VLANs & Trunking:
Segment networks into isolated broadcast domains, enhancing security.
Misconfigurations can lead to attacks like VLAN hopping via switch spoofing or double tagging.
Tagged VLANs help prevent unauthorized access between segments.
ARP spoofing: Attackers send fake ARP replies to associate their MAC with a victim’s IP.
MOII & MAC Security: MAC spoofing detection is used to enhance Layer 2 security.
Network Layer
IP Addressing: Enables devices to communicate across different networks using IPv4 or IPv6.
IPv4 vs IPv6:
IPv4 uses 32-bit addresses; IPv6 uses 128-bit, allowing vastly more unique addresses.
IP Classes organize IPv4 addresses for network segmentation.
Documentation IP Blocks (RFC 5737):
192.0.2.0/24 (TEST-NET-1)
198.51.100.0/24 (TEST-NET-2)
203.0.113.0/24 (TEST-NET-3)
Reserved for testing; not for production use.
IPv6 Documentation Prefix:
2001:DB8::/32A special IPv6 block reserved by the IETF (RFC 3849) for documentation, examples, and training.
Prevents misuse of real IPv6 addresses in books, blogs, and lab setups.
Avoids confusion, accidental traffic leaks, and security risks.
Non-routable; any traffic to this range is dropped by routers.
Recognized globally as a safe prefix for educational use.
Can be subnetted (e.g.,
2001:DB8:1::/48) to model real-world configurations.Similar to movie phone numbers starting with 555—looks authentic but never connects.
Ensures documentation is professional, consistent, and conflict-free.
Example addresses:
2001:DB8:1234::1/642001:DB8:abcd:5678::/64
Private Addresses: 100.64.0.0 - 100.64.128.255 (used by ISPs and Tailscale; avoids collisions).
DHCP Reservations:
- Assign fixed IPs without relying on sequential allocation.
Routing:
Direct tapping of Ethernet wires is expensive and impractical; port mirroring on destination devices is preferred.
Layer 2 MITM attacks are easier to detect; higher layers offer better protection.
Routing protocols: OSPF, BGP, ISIS (mostly for carrier networks).
Common Routing Attacks:
BGP: Prefix hijack, route leaks, manipulation
OSPF: LSA injection, falsification, evil twin, LSU spoofing
ISIS: Route spoofing, session hijacking
Transport Layer
Protocols: TCP, UDP, and ICMP form the core of the Transport Layer.
NAT (Network Address Translation):
Allows multiple devices to share a single public IP.
the purpose of NAT is to saves IPv4 addresses and hides internal network structure for security
Types: Static NAT, Dynamic NAT, PAT (NAT Overload), Port Address NAT.
Packet Wrapping
TCP traffic can be encapsulated inside UDP packets for tunneling.
Reliability is still ensured through TCP sequencing and acknowledgments.
Useful when networks restrict or block certain protocols.
Enables communication to pass through firewalls, NAT devices, or strict network policies.
Common in VPNs and tunneling tools where flexibility and traversal of blocked paths are required.
Security & Protections:
Maintain ACLs to control access.
Change default ports to reduce attack surface.
Use VPNs and tunneling to secure communication.
- Packet Analysis:
Tools: tcpdump with drivers like usbpcap and ncap capture interface packets for analysis.
- Real-World Topologies:
Designed for carrier gateways and high availability networks.
For real carrier gateways & high availability infra networks
- TCP Flags:
PSH (Push): Packet must be processed immediately.
URG (Urgent): Specifies high-priority packets
- ICMP, Ping, and Traceroute:
Used for error reporting, diagnostics, and status messages.
Traceroute works by incrementing TTL to map the route to the destination.
WiFi Highlights
WiFi operates at Layer 2 (Data Link), while radio waves act as the physical carrier medium at Layer 1.
Security Protocols:
WPA2 (non-PKS versions) can potentially be decrypted if misconfigured.
RADIUS and other authentication protocols manage secure access.
Miscellaneous / Performance Highlights
Ethernet Performance: CAT cables can support speeds up to 58 Gbps in optimal conditions.
Data Flow: Every packet leaving a device enters the network for processing.
Passive Wiretap: Operates at Layer 2 and can intercept traffic without detection, highlighting the importance of network security
The session ended at the Transport Layer, while the higher layers :- Session, Presentation, and Application were left out. These will be covered in Application Security (AppSec), keeping the focus here on core networking basics first
Hardware Arsenal
View the slide deck for this talk here
What is it?
Hardware/Hacking Arsenal → Tools designed for specific protocols with compromise as the ultimate goal.
Focus → How much can you breach without breaking cover?
Uses → Military operations, physical red teaming, and fun research.
P4wnP1 A.L.O.A
Turns Raspberry Pi Zero W / Pico W into a powerful, low-cost pentesting tool.
(Reference:-https://www.raspberrypi.com/documentation/)
Acts like a WiFi Rubber Ducky with HIDScript (DuckyScript-style payloads).
(Refrence:-https://github.com/majdsassi/Pico-WIFI-Duck)
Can emulate keyboard, mouse, storage, and more for red teaming & research.
Pwnagotchi
AI-powered WiFi sniffer (A2C + bettercap) that learns from its environment.
Captures WPA handshakes & PMKIDs (saved as PCAPs for hashcat)
PMKID (Pairwise Master Key Identifier) is a unique value in WPA/WPA2 Wi-Fi that speeds up roaming but can also be captured for offline password cracking.
A digital pet for hackers running on Raspberry Pi Zero W/2W, 3, and 4.
(Refrence:-https://github.com/JakerHuber/Jakes-Pwnagotchi-Tutorial.git)
Flipper Zero
Portable multi-tool for pentesters & hackers in a toy-like body.
Hacks radio, access control, hardware, and more.
Open-source & customisable with modular extensions.
PortaPack (for HackRF)
Add-on with touchscreen, controls, SD slot, clock, and case.
Turns HackRF into a portable spectrum explorer (few MHz – 6 GHz).
(Refrence:-https://github.com/pavsa/hackrf-spectrum-analyzer.git)
Runs on USB battery + proper antenna. (Can be misused for illegal activity)
Keyless Entry & Rolling Code
Used in cars & garage doors for remote lock/unlock.
Rolling Code: generates single-use passcodes so codes don’t repeat.
Exploit angle → If the signal doesn’t reach the car, the sequence can be intercepted & abused.
USB-C
24-pin reversible connector, replacing older USB types.
EU mandate:
Phones, tablets, cameras & headphones → by Dec 28, 2024
Laptops → by Apr 28, 2026
Goal: One universal charger/cable.
BAD USB-C (Overview)
ESP32 Pico-based USB-C implant for executing keystrokes.
Can run scripts, payloads, admin/root commands.
With WiFi onboard, it can even bypass air-gapped systems (requires physical access).
Example:
BAD USB-C is an ESP32 Pico-based implant disguised as a USB-C device. It behaves like a normal USB peripheral, but in reality, it executes automated keystrokes and connects over WiFi.
How It Works
Physical Access → Connect the BAD USB-C to the target computer.
Remote Control → Connect to the device from your laptop, VM, or even a smartphone hotspot.
Payload Execution → BAD USB-C injects keystrokes on the victim’s machine as if typed by a user.
Example Attack Scenario
Prepare a payload script (PowerShell or Batch).
BAD USB-C executes automatically once plugged in:
Opens Command Prompt or PowerShell.
Elevates to Administrator (via keystroke sequence).
Executes your script, e.g.:
Copies documents, credentials, or browser data.
Compresses them into a hidden archive.
Sends them back over WiFi.
Air-Gapped Bypass
An air-gapped system is normally secure because it’s isolated from any network. BAD USB-C, powered by ESP32 Pico with WiFi, can still bypass this protection.
Injects payloads via keystrokes (e.g., open CMD/PowerShell).
Collects files (docs, creds, logs).
Exfiltrates data over WiFi directly to the attacker’s device.
Stealth mode: BAD USB-C can connect to a hidden SSID (like a mobile hotspot) for operational security.
Example:-
Plug BAD USB-C into an air-gapped PC → it runs a script to zip “.docx” files → connects to your hidden mobile hotspot → sends data over WiFi to your laptop.
The air-gap is silently bypassed.Key point: Unlike normal USB-C, BAD USB-C is both injector and covert channel, making it far more dangerous.
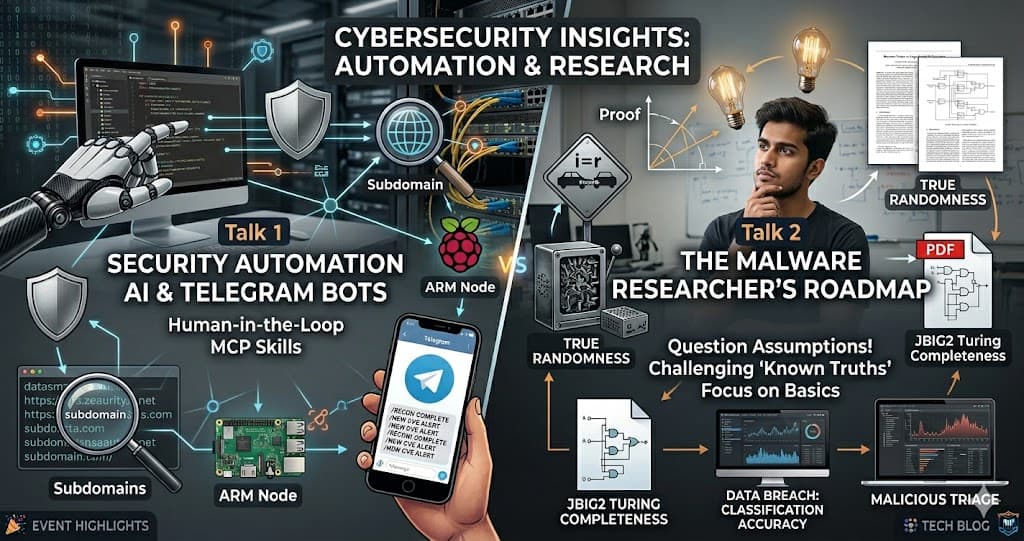
The session showed a clear journey of how communication has evolved and how today’s networks work.
Along with this, the hardware segment showcased practical tools like P4wnP1, Pwnagotchi, Flipper Zero, and PortaPack, giving a glimpse into hardware hacking and security.
![Lecture 4 - Rediscovering Process Scheduling [Part - 1]](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1765604682888%2F80e6cf20-aded-4aac-8c75-affdd35615b2.jpeg&w=3840&q=75)
![Lecture 3 - Reinventing MMU [Part - 2]](/_next/image?url=https%3A%2F%2Fcdn.hashnode.com%2Fres%2Fhashnode%2Fimage%2Fupload%2Fv1763234243271%2F6bb1c737-9def-4975-a06d-7ca59791c881.png&w=3840&q=75)